Latest Blogs
Cybersecurity
Ramsha Khan
May 19, 2026
In-House vs. Managed SOC: A CISO’s Decision Framework for Your Business in 2026
Read More...

Video Marketing Trends to Follow in 2020
We’ve seen developments in video marketing evolve over the years, from 30-second ads to viral videos to vlogs and live streams. In fact, new technologies have paved the way for more immersive video formats, such as experiences in 360 degrees, ephemeral videos and shoppable videos. According to HubSpot, ‘78% of people watch online videos every week, and 55% view online videos every day.’
Video marketing trends have advanced greatly from 30-second ads to viral videos to vlogs and live streams. Now the path is paved for more captivating video formats such as 360 degrees, shoppable and ephemeral videos due to the new technologies.
New trends are coming up this year, and some are fading away. Video marketing is one of the top social media marketing tips to revamp your marketing strategy
Here are some of the trends you should consider.

Live media is one of the most engaging concepts out there. This is due to living interactions with real people.
If you are a Snapchat or Instagram user, you might have noticed that a lot of people whom you follow go live numerous times a day. These lives consist of people answering questions sent by other people in real-time. Some might also take dares from other users to do. This content is meant to be interactive.
You can save your life using Instagram’s feature; however, people will not revisit a Livestream, which is why video style is so effective.
Remember, when live radio and television used to be famous among people around the world, live videos recreate the same type of experience by giving people the same phenomenon all around the world at the same time. Live videos are a trend that is here to stay, so it is best to experience with the type.

One of the biggest trends evolved in the past few years is selling on social media. This has made the interactions between vendors and customers easier and simpler, which makes it up to date to the on-demand industry. A lot of businesses benefit through social media content.
There are plenty of videos that allow users to shop on the spot without having to search up anything. They may not have to search for the product manually. They must click on the product, and they will be redirected to the respective site.
This trend should not be ignored as recently in 2020, we have seen an increase in the likeliness of customers wanting to purchase a product after watching a video about it.

Another major trend is the interactive 360 videos. We can experience wide-ranging musicals, sports games, and iconic locations using it.
Interactive videos might not work every time, but there are different ways of using virtual reality to make it engaging and fun. An example of this could be of an interior design company that would make their audience experience a virtual tour of their projects using virtual reality.
As AR and VR continue to grow, we expect to see a more immersive and futuristic style of videos like these. If you are ambitious, you can do something like this yourself.
To captivate the customer base, making a video on the product can be quite challenging but very helpful for your business.

Sometimes you are in public and would watch a soundless video. This is a trend evolving which prefers to show rather than explaining through sound.
Social media users would like to watch with no sound, or sound can be accommodated using subtitled videos. Creating videos that do not need sounds to be understood or using captions would be a wise idea.
These videos can help us understand different scenarios, such as appearance, mechanism, composition, and involvement in daily life. Specifically, rearranging Ikea furniture, silent video trends, and immersive ads trend.

After seeing the growth of vlogging channels on sites like YouTube, vlogging continues to develop. People document their everyday life, share their experiences, talents, or to express their feelings and personality to the public using vlogging. Actors and influencers use vlogging to communicate with their fan base. We have also seen a lot of brands branch into vlogging.
Celebrities and influencers reach out to their followers using vlogging. Companies can interact with their customers with the help of vlogging. Vlogs are a more authentic and unfiltered version of your brand as compared to a company produced project. This gains the trust of the consumer and helps personify your brand.

Publishing ephemeral content in effective ways is one of the advantages of social media stories. After 24 hours of posting stories, they are automatically removed from the site as they comprise of texts and pictures.
These have become a new form of vlogging, which is low-fi and does not need the extra effort of editing. Stories will continue to gain fame as they are being implemented by sites like YouTube, Twitter, and Instagram.
Saima Naz
May 14, 2020

Top 8 Facebook Ad Hacks to Reduce Costs and Increase Co...
Facebook is undoubtedly a persuasive platform for advertisers for countless reasons, including potent targeting options and reasonable costs.
Done properly, a Facebook ad campaign can significantly improve your conversion rate, the number of website visitors and your overall performance. But to make your advertisements effective on this well-known social media platform and know what advertisements to run and where can take some time and money. So, if you are looking for better ways to bring the best results, you should do proper research. Any of your Facebook ad costs depend on a number of factors, including your audience, industry, goals, and optimization settings.
Here are the top 8 hacks which can drastically reduce costs and increase conversions.
A strategy is a must even before you think about your Facebook optimized ads. To succeed, you must know your right audience. A thorough understanding of your targeted audience includes what they like, share or mostly respond to. When you narrow down and focus on targeting the right audience, you can greatly cut competition from other brands running advertisements to comparable audiences. You should precisely know that you are in a bidding war with various other brands and you just need to bid on who you really want to reach. So, before you begin optimizing Facebook ads, check your ad reports to see if you target the relevant audience.
Facebook experts do not give any specific claims or practices about the frequency of showing the same ad to a single user. But we should also consider the fact that people should not turn off your ad or label it as spam after they get annoyed by seeing it too many times. Do a little research and try to estimate how frequently people will notice your ad when it’s shown to them. A simple way of doing this is by rating the ad’s visuals. You should show each ad a minimum of 3 and a maximum of 10 times in Facebook’s newsfeed. For the sidebar, you could jump to a minimum of 10 and a maximum of 40 ads.
Time frames matter the most in Facebook ads. If you ever noticed, there are some days and time frames when your posts get more likes and those days outperform as compared to the rest of the days; that’s when you need to set up your ad campaigns. No campaign runs successfully 24/7. So, analyze which days perform better in terms of conversions at the lowest CPA. You can go to your Facebook Ads Manager reports and use the Breakdown menu to break down your campaigns by day.
People nowadays are too caught up to give time to a long-written copy. Pressed for time, they only tend to skim the lengthy text. So, the tricky part of this is creating a compelling ad within this short copy. Keep your brains all active and write a two-line (or maybe one) copy that sums up all the specific points and also a CTA. So, give your best shot and prepare a catchy and concise ad copy while retaining all the elements of a ‘good’ ad.
Facebook messenger ads are comparatively cheap if set up rightly and effectively. They show up on the home screen of the Messenger. Placement of the ad also plays an integral role. So, if you are already using Facebook ads and their manager, then the placement of the ads become quite simple. You may also use some of the advertisement material which is already there. The biggest benefit of Facebook Messenger ads is that you directly send people to your website or initiate conversations in order to connect with the users. The good thing: all these conversations are handled by bots, which direct users to the best offers.
People tend to leave abandoned checkouts for unknown reasons. So, retargeting them with videos can get them back, which results in increased conversions. So, what you need to do is put a video on Facebook about what it is like to be a customer and what benefits and value they may get in return. This video is intended to directly help them see what they’re going to get, and the video format is perfect for bringing this kind of personalized message across. This is an excellent way to get them to rethink stuff and, ideally, become a bona fide customer.
If your ads are placed rightly, they can bring a great increase in the conversions and hence results in cost reduction. When it comes to serving social media ads, Facebook placement is the original gangster. Not all placements will be available for mobile, and not all will be available for desktop. You need to place your ads accordingly, keeping in mind your target audience. Some Facebook ad formats and placements may better serve your goals than others, depending on your campaign’s priorities.
Adidas, for instance, determined that using video with the collection feature of Facebook would be a useful way to display its Z.N.E Road Trip Hoodie’s various features. As a result, Addidas has been able to reduce conversion costs by 43 percent.
Once you become sure of the placement and format that is working best for bringing conversions, you can raise your bids on top-performing placements. But if an ad placement doesn’t meet your targets, you may remove it from your ad set.
Although A/B testing offered by Facebook isn’t the best thing to rely on as it is difficult to use and not entirely accurate, it is still good to run an A/B test with the ads you have. It is always better to be on a safe side with at least some data rather than none. With Facebook A/B testing options, you’ll get a good idea on what’s working and what’s not.
Saima Naz
May 8, 2020

Top 6 Python Libraries for Machine Learning
Recently, with the push in the AI sector, machine learning and deep learning have been on the rise and the early adopters of these technologies are starting to see their results. More and more businesses have hopped onto the bandwagon and started investing their time and effort in fully understanding this untapped domain’s potential.
Here are our top picks:
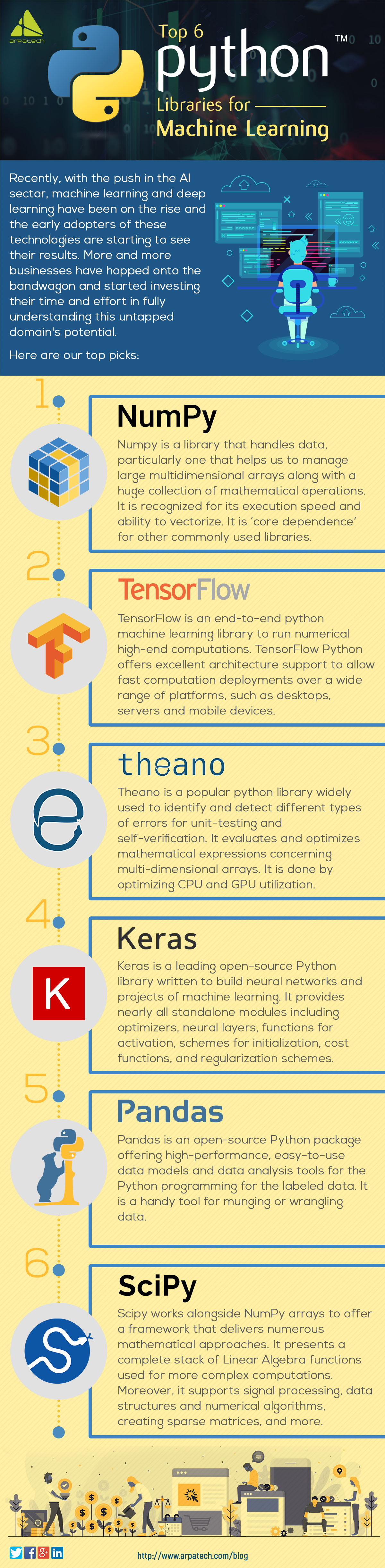
Numpy is a library that handles data, particularly one that helps us to manage large multidimensional arrays along with a huge collection of mathematical operations. It is recognized for its execution speed and ability to vectorize. It is ‘core dependence’ for other commonly used libraries.
TensorFlow is an end-to-end python machine learning library to run numerical high-end computations. TensorFlow Python offers excellent architecture support to allow fast computation deployments over a wide range of platforms, such as desktops, servers and mobile devices.
Theano is a popular python library widely used to identify and detect different types of errors for unit-testing and self-verification. It evaluates and optimizes mathematical expressions concerning multi-dimensional arrays. It is done by optimizing CPU and GPU utilization.
Keras is a leading open-source Python library written to build neural networks and projects of machine learning. It provides nearly all standalone modules including optimizers, neural layers, functions for activation, schemes for initialization, cost functions, and regularization schemes.
Pandas is an open-source Python package offering high-performance, easy-to-use data models and data analysis tools for the Python programming for the labeled data. It is a handy tool for munging or wrangling data.
Scipy works alongside NumPy arrays to offer a framework that delivers numerous mathematical approaches. It presents a complete stack of Linear Algebra functions used for more complex computations. Moreover, it supports signal processing, data structures and numerical algorithms, creating sparse matrices, and more.
Saima Naz
Apr 29, 2020

Why You Should Consider DIY Website Builders
A DIY website builder is a platform available online where by just signing up with your email address you have access to upload contents such as images, texts, slideshows, etc., on a blank canvas from which you can populate your website. DIY website builder not only gives access for the creation of web components but also cuts down the responsibilities of hosting your web page, so you don’t have to bother about technical details including configuration, security updates, etc.
Business executives, freelancers and entrepreneurs who like investing in e-commerce vendor assistance gets to build their bottom line ultimately. The collaborative approach to selection making gives license to both events to leverage their expertise because it pertains to the gradations of their enterprise.
The monthly subscription fees, these enterprises get the tools to build an online store or any static internet site where more complex tasks including hosting, uptime, security, software updates are all looked up by SaaS vendors.
After the web construction is done for the clients or themselves, business executives are often found frustrated because of the inefficiency of the website they built. They are unable to make changes to their website’s online design, nor can they change or alter text, links or menus easily. Moreover, they cannot add services like appointment scheduling or even e-commerce options without high hand expenses.
Fox describes constructing your own billing device as an “iceberg issue”. In the beginning, you see few primary troubles but once you have started, you identify all the complications which lie below the surface and eventually absorb a maximum of a while, lowering usual productivity.
Furthermore, business executives frequently encounter problems every day such as software program and system readiness, team subculture, and coding information, among others.
It’s been an ultimate decade of the widespread development of e-commerce in consumer market. With the growth of technology, there’s a boom in purchasing online trends which has empowered the purchaser brands.
With a sharp rise in e-commerce that has taken over B2B marketplace, these brands have shifted to B2C peers, in order to obtain modern technology so as to make buying experiences more competitive.
According to Research, the next huge wave of increase for e-commerce is within the B2B market, and with a view to take advantage of it, groups want to adopt DIY website competencies.
“B2B manufacturers are looking to create web sites that permit their customers purchase similar to they would from a B2C web site consisting of Amazon or Zappos,” he says.
Online shop builders help us with virtual information and IT help, facilitating us with accountability and dependability. The purpose of the net development assistant is to empower digital agencies, businesses, freelancers with tools that help to build an attractive web site. These Ecommerce Website Development Services have taken over the virtual world.




Saima Naz
Apr 25, 2020

7 Common Bloopers That Could Ruin Your PPC Campaign
There are a few common mistakes we often overlook within the realm of PPC, which can result in failed campaigns.
The telltale signs of PPC mismanagement can be recognized by the most experienced PPC experts.
But if you’re not a PPC specialist, you might overlook those indicators. Thankfully, these indicators and best practices are easy to resolve to make the most of your paid social media marketing campaign.

Poor account structure on Google Ads is the culprit when a PPC ad struggles to yield results. When defining your ad groups, make the keywords as specific as possible. Make use of accurate matches, negative keywords, and avoid broad matches that could lead to wasted clicks.
Words are incredibly important. If you don’t pay enough attention to things like bold headings, clear value propositions and strong, persuasive calls to action, then you’re probably missing out on business.
Throughout, managers should have only about 7 to 10 ad groups per campaign and just about 20 keywords per target group.
Negative keywords are the reverse of the keywords you target. They help you to ensure that only relevant search terms display your ads.
Your quality score and your CPC are used to determine the position of your search auction and ultimately decide your overall ad spending. The lower your quality score, the costlier your campaign will be.
It’s important to reach out to new audiences, but you shouldn’t overlook those people who have already interacted with your brand. People who already know you are more likely to trust you and pay more attention to your paid ads.
To accelerate conversions, a landing page is crucial. If your PPC advert drives people to your business’s home page, they’re likely to move on to a competitor.
Saima Naz
Apr 14, 2020

How to Safeguard Your Cloud Security From Next Cyber-at...
This year has been a very exciting year for cloud computing, and it is only going to get bigger in the years ahead. It’s quite clear why businesses are preferring cloud computing; it is easier, more affordable, and it is easier to use third-party cloud services rather than maintaining your own data centers on your own premises.
Due to the shift in cloud computing, businesses, irrespective of size, have been allowed to access scalable resources, lower their IT costs, and cut down the on-site load of their IT infrastructure.
No matter what size your business is, it is a looming threat of hackers to steal information. So, in a situation like this, businesses should act responsibly and ought to be prepared when it comes to securing their data from hackers.
It is indeed possible to keep your data secured on the cloud, but there is no doubt that cyber threats are evolving and cloud servers are their key target.
Here are a few tips on how you can safeguard your cloud security from cyber-attack!
The first and most important thing to do to prevent your business from a cyber-attack is to carefully scrutinize the internal and external vulnerabilities your business encounters when it comes to hackers. What you need to do is prohibit the way from where you think a hacker can gain entry into your system, and that can be done by identifying your weaknesses. The most apt way to do it is to be informed about the several cyber fraud schemes and threats, such as malware, system hacking, phishing, and various others that a business faces. Once you know your own vulnerabilities, you can handle them in the following ways.
To date, encryption is the best way to protect the confidentiality and privacy of your data. Keep in mind that hackers are always looking for standard company-held information, whether they are bank-routing digits or employee social security numbers. So, remember to take measures to get this information encrypted. You can guard your information by switching to full-disk encryption tools, which come by default with most of the operating systems. It should not take more than a minute to switch the encryption of these devices on, and all files on your drive will be encrypted without slowing down.
Moreover, end-to-end encryption ensures the best level of protection for sensitive information and documents. As a result of end-to-end encryption, encryption is carried out on the client side so that files are encrypted before they leave your device and continue to be encrypted till they reach the supposed recipient.
This is the most common warning you must have heard a hundred times. But people give it a deaf ear and create easy-to-remember passwords, which is why their accounts get hacked. The most familiar source of cyber-attack is password prediction, yet it is the most preventable one. The tip is to think strategically when you create them. Moreover, keep changing the password often. Never try to reuse an old password or use the same password for various accounts. Do not keep any password in the cloud or a text file. Furthermore, complement your password with a two-factor authentication requirement for accessing sensitive company information services.
It would be extremely foolish to save a little amount of money and go for an inexpensive cloud. The reduced cost public clouds might look tempting, but they are frequently riddled with security threats and vulnerabilities. Although private clouds are expensive, they have minimal entry points and more stringent safety measures in place. Moreover, these private clouds are in a fairly good position to monitor your account while allowing them to preemptively deflect attacks and minimize their impact.
The transference of data back and forth to the cloud travels through the internet, which is where your data becomes most vulnerable. Note that data must be encrypted in the cloud environment at all stages of transfer and storage.
So, be sure about the channels you pick for data transfer, and make sure the data is encrypted before it is sent out anywhere. Protecting data transfer channels is a convenient way to prevent any sophisticated cyber-attacks, which most people usually overlook.
ERP software applications are accessed through Application Programming Interfaces (APIs) on the cloud. Any cloud developers should ensure that the clients access the application through secure APIs, which requires restricting the range of IP addresses or giving access only through corporate networks or VPNs. However, it is quite difficult to implement.
So, just to be sure, perform an evaluation of the existing API to check for any vulnerabilities. Analyze ways to boost it, or you can simply switch to an API that is more secure.
You cannot protect what you cannot see. Enabling continuous monitoring and logging is a key pillar of any strong cloud security strategy. Even with strong configurations and access controls, threats can still slip through undetected without proper visibility. To maintain visibility across your cloud environment, the following should be part of your setup:
Proactive monitoring allows your team to detect issues early and respond before any serious damage occurs.
As cloud environments grow in complexity, keeping track of misconfigurations and compliance gaps becomes increasingly difficult. Cloud Security Posture Management (CSPM) tools continuously assess your cloud infrastructure against security best practices and regulatory standards.
CSPM helps you:
Without CSPM, even a small misconfiguration can open the door to a major security breach.
Ransomware attacks targeting cloud environments are on the rise. A strong backup and recovery strategy is important for any cloud security plan. To protect your data from ransomware and unexpected failures, maintain:
Testing your restoration procedures on a consistent basis strengthens your business’s ability to recover without suffering prolonged downtime after an attack.
No security strategy is complete without a clear plan for when things go wrong. An incident response plan prepares your team to act quickly and decisively in the event of a cloud security breach, minimizing damage and reducing recovery time.
A solid incident response plan should include:
When it comes to breach response, time is your most valuable asset, and every second your team acts faster, the harm caused is limited.
One of the most effective ways to limit the impact of a cyber-attack is by ensuring that users, systems, and applications only have access to what they need. This principle is known as least privilege and is a key part of the Zero Trust security model.
To implement least privilege and Zero Trust effectively:
Zero Trust challenges the outdated notion that users inside a network can be trusted, treating every access attempt as a potential threat until proven otherwise.
Regularly testing your cloud environment is the only way to truly know how well your defenses hold up against real-world attacks. Think of penetration testing as hiring someone to break into your own house before a real burglar does. Your security assessment plan should cover:
Regular assessments give you an honest picture of your security posture and help you stay one step ahead of evolving threats.
With cloud technology, where there are conveniences, there are certain types of risks as well. By understanding and implementing these necessary steps, one can smartly safeguard one’s cloud security, and cyber threats can be easily thwarted. If the cloud technology is dealt with rightly, it can be the most cost-effective and secure place.
Cloud security is not a destination but an ongoing journey that demands consistent effort, attention, and adaptation. Cybercriminals are becoming increasingly creative and relentless in their approach, and businesses that only react after an attack has already happened are fighting a losing battle. Those who make it a point to regularly review their environments, keep up with the latest threats, and have the right security tools ready will be in a far stronger position when attackers eventually come calling. In a world where cyber threats never sleep, staying one step ahead is not just good practice; it is what keeps your business alive.
Ultimately, the strength of your cloud security comes down to the decisions you make every day, from how you manage access and encrypt data to how quickly you respond when something goes wrong. Organizations that treat security as a core part of their cloud strategy, rather than an afterthought, will thrive safely in the digital age. Ready to strengthen your cloud security? Contact us today and let our experts help you stay protected.
Saima Naz
Apr 8, 2020